Resultados de la campaña de monitorización puntual sobre accesos web inseguros

Acabamos de terminar una nueva campaña de monitorización puntual sobre el perímetro de nuestros clientes, en esta ocasión enfocada en posibles accesos web inseguros. Y una vez más se demuestra la gran importancia que nuestros clientes dan a la seguridad.
Este proceso es inocuo para el cliente ya que se efectúa de manera remota y no intrusiva, para lo que utilizamos tecnología propia y/o de terceros.
Hemos querido realizar una campaña combinando vulnerabilidades conocidas, como los accesos web inseguros, con nuestro referencial LEET. Para ello, nos hemos centrado en identificar si disponen de un certificado digital válido y seguro.
El objetivo de esta campaña es que todas las conexiones web sean seguras y de confianza, protegiendo la confidencialidad de los datos. Con este fin, hemos analizado 3 parámetros: si se dispone de un certificado de una CA (Autoridad certificadora) reconocida, si éste se encuentre en vigor, y cuál es el algoritmo de cifrado utilizado.
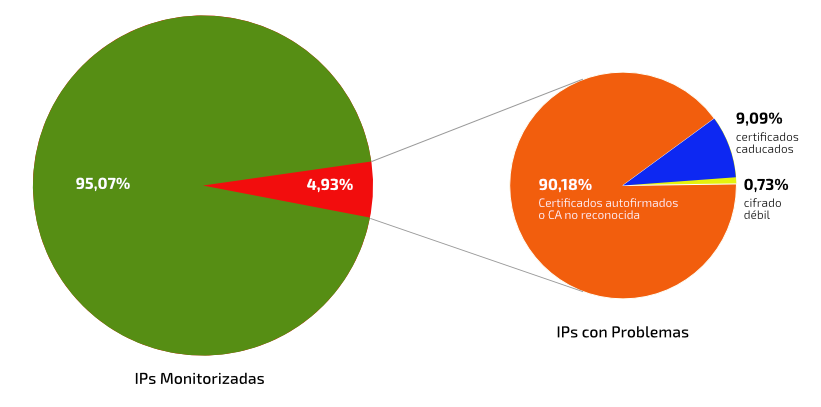
Se han monitorizado alrededor de 25.000 IPs, en las que se han localizado:
-
9 IP con certificados autofirmados o de una CA no reconocida
-
112 IP con certificados caducados
-
1111 IP con un algoritmo de cifrado débil
Estos hallazgos pueden tener un reflejo directo en la calificación de LEET Security del cliente, al incumplir uno de los controles del "Dominio 9: Controles de red": “Mantenimiento de la confidencialidad sobre redes públicas”, aplicable a partir de la calificación B.
Estos datos indican la gran importancia que nuestros clientes dan a la seguridad pues, en la mayoria de los casos (95%), hemos encontrado que se protege correctamente la información confidencial en las transmisiones abiertas.
Este sistema de monitorización, que combina las campañas puntuales y la monitorización digital de carácter periódico, amplía la utilidad de la calificación para conocer las debilidades y fortalezas propias, que es primer paso para una protección efectiva.
Por esto, la calificación de LEET Security es el método más exhaustivo, riguroso y fiable para determinar el nivel de ciberseguridad de un servicio de cualquier tipo de organización.
All you need is LEET!
Recibe nuestras notificaciones desde este enlace

