Una reflexión sobre el ataque a Kaseya
Controles y capacidades esenciales para salir bien librado de un ciberataque
Recientemente hemos tenido la oportunidad de atender a un webinar titulado “The Kaseya Attack - What We Know and What We Must Learn”, organizado por una compañía que ofrece servicios de rating digital, bajo el lema de que estos hacen fácil entender y actuar sobre los riesgos.
Ha sido interesante conocer la historia del incidente, que comenzó a fraguarse el 6 de abril, con la notificación a Kaseya desde el DIVD (Instituto Holandés de Divulgación de Vulnerabilidades) de que habían detectado 7 vulnerabilidades en su software de gestión y monitorización remota VSA. El 8 de mayo, Kaseya lanzó los parches para 4 de ellas, y el 26 de junio finalizó los de los 3 restantes, procediendo a la actualización de su versión SaaS, y programando la actualización de las versiones on-premise para el 7 de julio.
Pero el ataque llegó el 2 de julio.
Ciertamente, Kaseya ha hecho un gran ejercicio de comunicación, y en tan solo 4 días, el 98% de las instalaciones de VSA estaban paradas hasta que la compañía realice el despliegue de los parcheos apropiados.
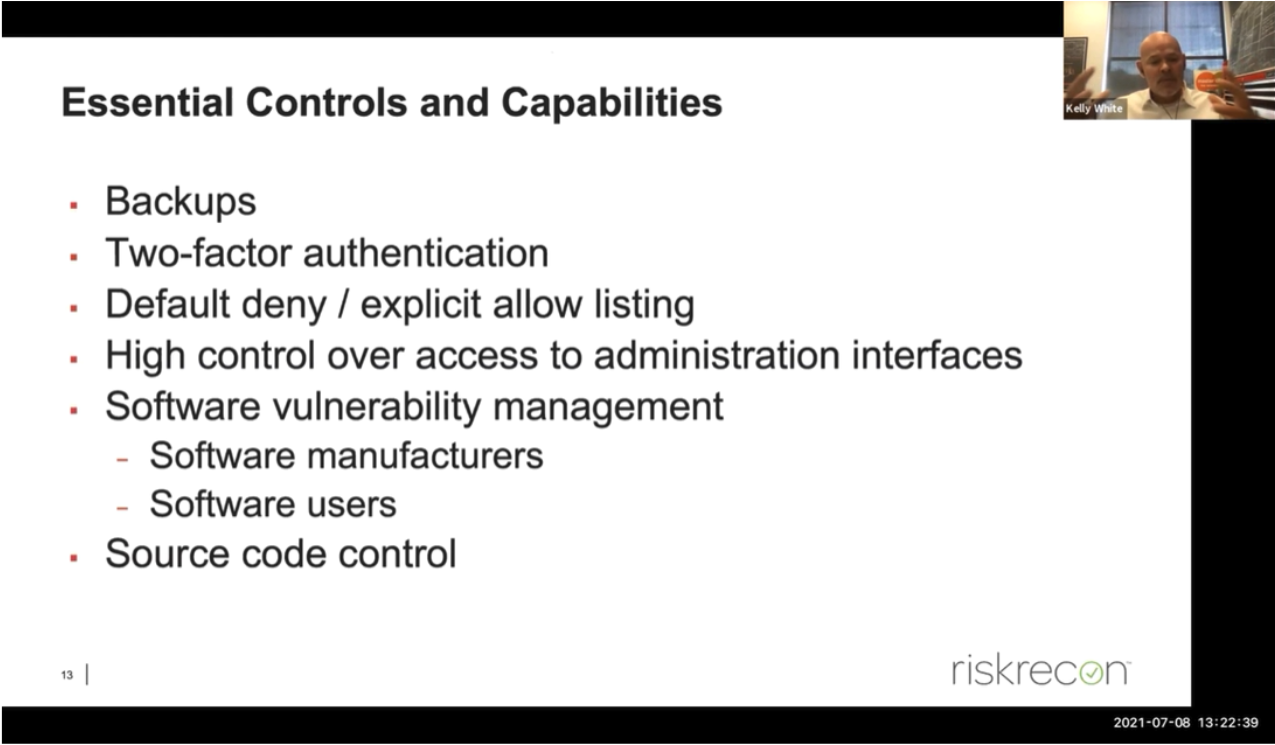
Lo más significativo del webinar, aparte de la interesante narrativa del curso del incidente, es el resumen que nos proporcionan sobre los Controles y Capacidades esenciales que deben estar implementados para tener un mejor posicionamiento de ciberseguridad en la organización:
-
Copias de seguridad
-
Autenticación de doble factor
-
Listas blancas de IPs/URLs permitidas / denegación por defecto
-
Riguroso control sobre las interfaces de administración
-
Gestión de vulnerabilidades, tanto en el software de los sistemas como en las aplicaciones de usuario
-
Control del código fuente
Pues bien, de todas estas condiciones, los servicios de rating digital, como los prestados por la organizadora del webinar, solamente pueden llegar a evaluar si en la compañía se están utilizando algunas versiones de software o aplicaciones que figuren en listas públicas de vulnerabilidades (no era el caso del VSA de Kaseya, puesto que, hasta el incidente, el DIVD solamente lo había notificado al fabricante). Por lo tanto, este rating digital no puede ofrecer una valoración realista sobre las capacidades de que disponen las organizaciones evaluadas.
Esto nos hace aun más conscientes de que el único rating que proporciona una información real y fiable es nuestra calificación de ciberseguridad, que tiene en cuenta todos esos controles y capacidades esenciales, y otros muchos que no lo son menos, como, por ejemplo, los programas de concienciación del personal, que es en muchas ocasiones quien abre la puerta pulsando sobre enlaces indebidos.
Las características de este incidente hacen que pueda considerarse un Zero Day, por lo que cualquier organización que utilizase la versión on-premise de VSA se habría visto afectada. No obstante, aquí se ve cómo la calificación ofrece una visión muy diferente, ya que uno de nuestros controles requiere, necesariamente y desde el nivel inferior, que “Todas las copias de seguridad tienen, al menos, un destino de copia que no es direccionable de forma continuada a través de llamadas al sistema operativo”, con lo que se garantiza que un ramsomware no secuestra también la información de respaldo.
El rating digital es un buen complemento, no vamos a negar sus beneficios. Pero resulta sorprendente que se intente posicionar como la herramienta definitiva para la gestión de riesgos de proveedores. Nos permite, eso sí, una observación más continua y automatizada del perímetro que la organización tiene expuesto a ataques desde el exterior, pero de ninguna manera puede dar a conocer su preparación y capacidad de recuperación en caso de incidentes. Como tal complemento es utilizado para monitorizar a nuestros clientes que cuentan con servicios calificados, proporcionando ambos la combinación óptima para tener el único rating de ciberseguridad realmente fiable del mercado.
LEET Security – The ultimate cybersecurity rating
All you need is LEET!
Recibe nuestras notificaciones desde este enlace


