Documentary evidence rating
Security program assessment
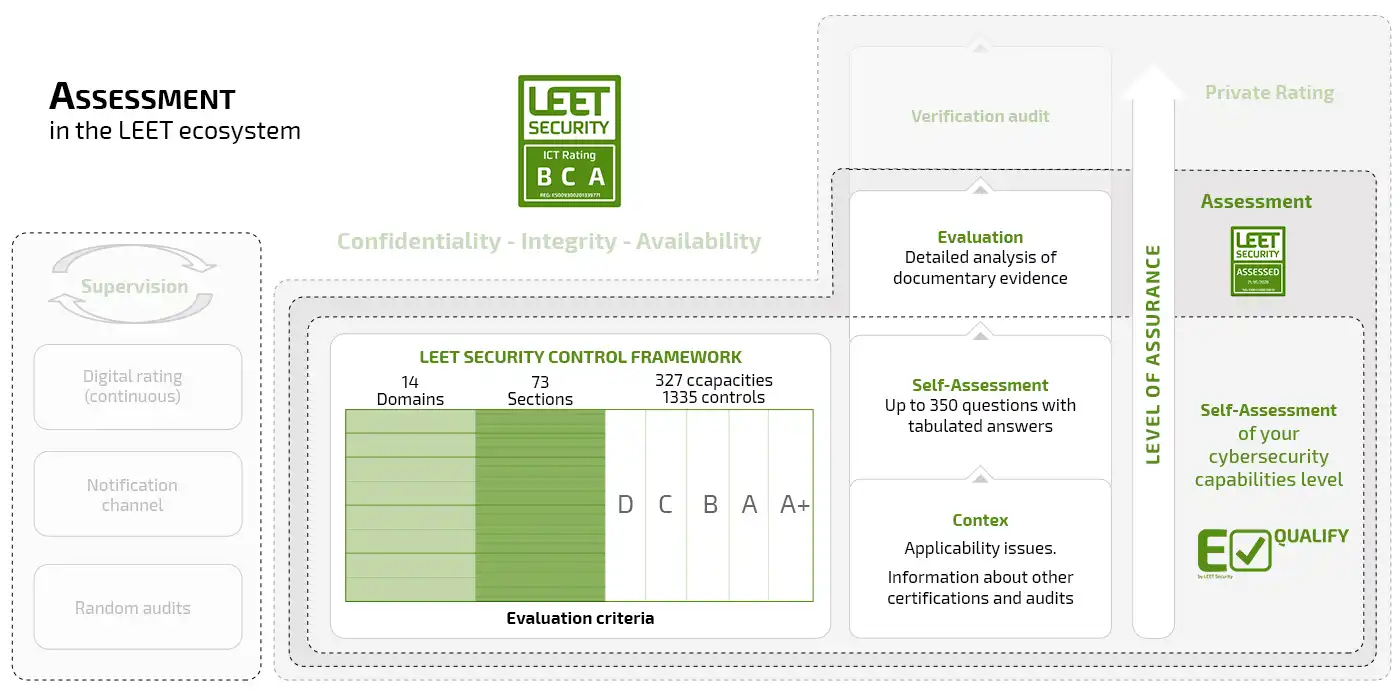
The Assessment is a cybersecurity-level rating that is service-focused, occupying an intermediate position between self-assessment and the Rating. The first is performed directly by the supplier without any type of evidence verification, while the second is granted following a rigorous audit process which is subject to monitoring mechanisms.

The Assessment and Controls Framework
Our Assessment service operates within LEET Security’s comprehensive control framework, comprising 14 domains and the five levels that define our rating. It begins with completing the self-assessment using the tool E-Qualify, in which you must answer all the questions corresponding to the target level selected, and identify the evidence and/or indicate how compliance with the selected controls is achieved.
Documentary Evidence
We request and evaluate documentation referring to:
Policies: A high-level description of the protection of the organization and its assets, as well as its incident management.
Standards or guides: implementation of policies to define how and where to perform the actions, with precise instructions.
Procedures: A description of the execution of different processes in accordance with the current regulations.
Based on the supporting documentation, our auditors evaluate the design of the controls and security measures, but not their operational effectiveness. However, they will verify that the execution of any process is carried out in accordance with established procedures. This method is similar to the employed for Type I reporting according to the ISAE 3402 / SSAE 16 methodology.
The evaluation process does not verify that the documentation provided is formally approved and communicated within the assessed organization, although our clients are required to take responsibility for both aspects.
Through this documentary review, a high level of reliability is provided to the assessment results. The assessment is granted across the three dimensions of Confidentiality, Integrity and Availability, and it is considered to have a validity of 12 months, given the rapid evolution of the Cybersecurity environment which requires a continuous review of the protection practices.
The report results may be used by the evaluated entity to demonstrate the level of security applied in the provision of its services. However, they do not constitute a full audit or continuous supervision as provided under the Rating service. Nevertheless, it offers a high level of confidence based on the verification of the organization’s security policies and procedures.

